Bitcoin Miners Are Publishers Protected by the First Amendment.

This post was originally published on June 24, 2022
Introduction
New York’s legislative assembly passed Bill No. A07389 on June 2, 2022, “establishing a moratorium on cryptocurrency mining operations that use proof-of-work authentication methods,” such as those used by Bitcoin, “to validate blockchain transaction” (hereinafter, the “Moratorium”). In other words, the Moratorium singles out for regulation one of many different types of cryptocurrency protocol consensus algorithms. And it singles out for regulation the users — “miners” or “validators” — of one specific type of algorithm.
The Moratorium, if signed into law by the governor, will violate proof-of-work miners’ rights to free speech under the First Amendment.
This is because proof-of-work miners engage in protected speech by broadcasting blocks of data across a protocol’s network. In fact, Bitcoin’s pseudonymous creator, Satoshi Nakamoto, explained that proof-of-work miners are engaged in “publishing” data for the world to see on an immutable, distributed “timestamp server.”1 The Moratorium singles out block publishers on proof-of-work protocols for a financial burden not borne by block publishers of protocols using other consensus mechanisms. As this article will show, such content-based differentiation is unsustainable under the Supreme Court’s First Amendment precedent.
The Moratorium thus provides a well-tailored case study to demonstrate that proof-of-work miners, especially Bitcoin miners, are engaged in protected speech under the First Amendment. If such a precedent could, one day, be established, it would provide a strong defense for the proof-of-work mining industry (and Bitcoin itself) against burdensome regulations such as the Moratorium, or even outright bans.
To be clear, the argument presented here is not that Bitcoin itself is speech. While that argument can be made (as Justin Wales expertly demonstrated in his foundational law review article Bitcoin is Speech: Notes Toward Developing Conceptual Contours of its Protection Under the First Amendment, and as Allen Farrington identified in Bitcoin is Venice), that argument is unnecessarily broad for purposes of addressing the Moratorium. And, more fundamentally, we are too early for such a transformative argument. The judiciary is simply not conversant enough with the technological, economical, psychological, and philosophical underpinnings of Bitcoin to render a well-reasoned decision on whether Bitcoin is speech. The time will come. But we will get there incrementally, as the judiciary learns and applies its growing knowledge to each case it considers and each precedent it creates about Bitcoin.
So let’s start that process here, with our first case study on Bitcoin as speech, in the narrow context of proof-of-work mining.
This article first establishes that miners in a proof-of-work protocol are engaged in speech as contemplated by the First Amendment. We’ll focus on Bitcoin as our example, because this is the Bitcoin Brief, and because of its overwhelming share of the proof-of-work market. Next, the article will examine how that miner speech is burdened by the Moratorium. Finally, the article will analyze the Moratorium under the different levels of constitutional scrutiny implicated by it.
Bitcoin Miners Publish Blocks of Data to an Immutable, Shared Database
The Role of Miners
To understand how Bitcoin miners are engaged in speech, one must understand what miners do, and how they do it.
This requires first dispelling a common misconception about Bitcoin miners. A miner’s primary job in the Bitcoin protocol is not to issue new bitcoins. Andreas Antonopoulos explains it best:
Mining doesn’t work to create bitcoin. That is not the purpose of mining; that is a side effect. The way I can prove it’s a side effect is that one day, there will be no new bitcoin. But guess what? There will still be mining. Even after the last satoshi (the smallest unit of bitcoin) gets mined, mining continues. It must continue because its purpose is not to create bitcoin but to provide security, to provide validation of all of the transactions and blocks according to the consensus rules. Generating bitcoin is a side effect that currently serves as a mechanism of reward, creating game-theory incentives to make sure that the validation is done right. Once you understand that and you realize what we’re paying for is security, it changes the perspective slightly.2
Changes the perspective, indeed. “Miners” aren’t really miners at all. They are transaction validators. As Darin Feinstein has pointed out, the term “miner” misrepresents the true nature of these nodes in the Bitcoin network: they are accountants auditing the ledger. The term “miner” conjures images of some type of dirty, industrial process of pulling resources out of the ground. That doesn’t sound like speech.
What does sound a lot like speech is Nakamoto’s description of the auditing process in his White Paper, the foundational document he used to introduce and explain his creation. Nakamoto did not use the term “miner,” but he did use the verb “publish.” Explaining how Bitcoin solves the double-spend problem, Nakamoto said:
The solution we propose begins with a timestamp server. A timestamp server works by taking a hash of a block of items to be timestamped and widely publishing the hash, such as in a newspaper or Usenet post [2-5]. The timestamp proves that the data must have existed at the time, obviously, in order to get into the hash. Each timestamp includes the previous timestamp in its hash, forming a chain, with each additional timestamp reinforcing the ones before it.3
And, to “implement a distributed timestamp sever on a peer-to-peer basis,” Nakamoto implemented “a proof-of-work system …, rather than newspaper or Usenet posts,” which democratized and decentralized the process of publishing blocks “to record a public history of transactions” on the time chain, or blockchain. 4
In other words, the role of Bitcoin miners is to “validate new transactions and record them on the global ledger.”5
Miners do this by aggregating together pending transactions that comply with the Bitcoin software’s rules and including them in a candidate block that the mining node will publish to the blockchain if it wins the proof-of-work contest for that round.
Proof-of-Work Primer
Let’s take a moment to examine how that proof-of-work contest functions, so we can better understand the data that miners are processing and writing to the ledger.
First, a simple analogy: miners compete to find a winning lottery ticket that grants them the ability to publish transactions to the blockchain.
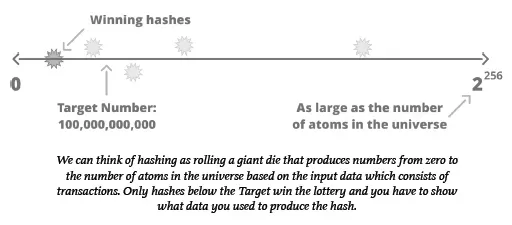
The concept behind Proof of Work is that you participate in a random process, similar to rolling a die. But instead of a six sided die, this one has about as many sides as there are atoms in the universe. In order to roll the die and generate lottery numbers, your computer must perform operations that cost you in terms of electricity.
To win the lottery, you must produce a number which is mathematically derived from the transactions you want to write to the ledger plus the value of the die you rolled. In order to find this winning number, you may have to roll this die billions, trillions, or quadrillions of times, burning thousands of dollars worth of energy. Since the process is based on randomness, it is possible for everyone to generate their own lottery tickets without a central authority using just a random number generating computer and a list of transactions they want to write to the ledger.6
Next, some details. To generate winning lottery numbers, miners use the SHA256 hash function, or algorithm:
The algorithm for proof of work involves repeatedly hashing the header of the block and a random number with the SHA256 cryptographic algorithm until a solution matching a predetermined pattern emerges. The first miner to find such a solution wins the round of competition and publishes that block into the blockchain. 7
Hash functions like SHA256 take in data and produce a large, random number, called a hash. A hash is like a digital fingerprint, because “the output is deterministic: you always get the same output for the same input,” and it is “infeasible to find two strings that hash to the same output.” 8
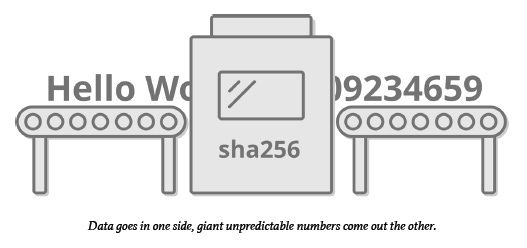
The SHA256 proof-of-work function is also a one-way function, meaning it is impossible to derive the input given only the output. But it is also asymmetric: given the input, anyone can run the algorithm once and verify the output. Thus, while it takes a miner many tries, using substantial compute power and energy, to produce a winning hash, it only takes a fraction of a second to verify the winning hash by the rest of the network.
To produce a hash for entry into the lottery, miners input the block header, plus a nonce, a number used only once. If the output hash is smaller than the target number (set by the Bitcoin software), the miner wins the right to publish the block that round.
So there you have it, that’s proof-of-work.
Proof of Work Miners Publish Facts and Opinions
With this background on proof-of-work in mind, we can now examine in detail the types of information miners publish. Data published in a winning block includes all pending transactions that fit within the block’s space limitation, metadata, and arbitrary data that the miners choose to include.
Specifically, miners write the following data into blocks.
- The list of transactions;
- The block header, which includes timestamp, the protocol version, previous block’s hash (winning lottery number), block’s Merkle root (hash of the list summarizing the block’s transactions), the difficulty target number, and the nonce (the arbitrary number used as part of input for the proof-of-work computation)9;
- The generation or “coinbase” transaction (not to be confused with the company by the same name) that rewards the miner, comprised of transaction fees, block subsidy (currently 6.25 bitcoin), and miner’s bitcoin address to receive transaction10;
- Coinbase data, which can include arbitrary messages from the miner.11
Although the mining process runs on computer code, block creation is not entirely predetermined. That is, it reflects deliberate choices that miners have made about which data to include. For example, miners can choose whether to include transactions with no fees (space permitting), and on which basis to include no-fee transactions.12
Miners also choose what messages to include in the coinbase transaction, from simply stating their name, to signaling support for proposals to upgrade Bitcoin’s software (called soft-forks).
Indeed, this signaling process for software upgrades is akin to voting, or, at a minimum, a non-binding straw poll. Before Bitcoin’s most recent upgrade, known as “Taproot,” mining pools (groups of miners pooling their hashing power together) included a message in their blocks signaling whether they intended to upgrade their software to accommodate the update. Miner votes were not necessary to implement the upgrade, but their indications of support meant that the transition would be a lot smoother.
Another example of a political message in coinbase data is found in the genesis block itself, the first block mined by Nakamoto:

This was a newspaper headline from the date of release. It was also a political statement about government interference in money. 13
Once a miner finds a valid hash under the target number, it broadcasts its candidate block (with all its data, including the proof-of-work solution, visible for anyone to verify) across the Bitcoin network for validation by the other nodes. If the proof-of-work is valid (the miner expended the resources to generate a valid hash under the target), the nodes will include the block in their copies of the blockchain. Through this process, miners publish data contained within the block to the decentralized blockchain in perpetuity.
The Supreme Court has long held “that the creation and dissemination of information are speech within the meaning of the First Amendment.”14
As explained above, creating and disseminating information are quintessential actions of proof-of-work mining nodes, not mere by-products. Miners exist to construct candidate blocks containing details of thousands of verified transactions, as well as other data, for publishing and inclusion in the protocol’s blockchain. This process of propagating verifiable facts across the protocol’s network of nodes is, therefore, speech. “Facts, after all, are the beginning point for much of the speech that is most essential to advance human knowledge and to conduct human affairs.”15
Additionally, blocks reflect opinions held by miners, which range from the practical to the political.
Proof-of-work miners, therefore, quite clearly engage in speech. “[I]f the acts of ‘disclosing’ and ‘publishing’ information do not constitute speech, it is hard to imagine what does fall within that category.”
The Moratorium Singles Out Proof-of-Work Publishers for Financial Burdens
The Moratorium is not an outright ban on proof-of-work algorithms. Instead, it places economic burdens on those mining companies running proof-of-work algorithms. But “[l]awmakers may no more silence unwanted speech by burdening its utterance than by censoring its content.”17
The Moratorium burdens proof-of-work miners by preventing access to lower-cost sources of electricity (for example, natural gas power plants). As currently drafted, it requires the New York Department of Environmental Conservation (“DEC”) to deny air pollution permits to any
electric generating facility that utilizes a carbon-based fuel and that provides, in whole or in part, behind-the-meter electric energy consumed or utilized by cryptocurrency mining operations that use proof-of-work authentication methods to validate blockchain transactions.18
And renewal applications will not be granted to these same carbon-based electricity providers if they seek contracts that would increase the energy consumed by proof-of-work miners.
Electricity is the necessary input of any data center, and represents the vast majority of any mining company’s operating expense. By limiting new and increased contracts for behind-the-meter electricity at carbon-based power plants, the Moratorium forces proof-of-work miners in New York to find alternative sources of energy, which are often more expensive. The Moratorium thus imposes a significant economic burden on proof-of-work miners — a burden not imposed on other data center operators or cryptocurrency protocol validators — solely due to the content of the data they process and publish (e.g., solutions to proof-of-work algorithms and transactions generated pursuant to the rules of the respective proof-of-work protocol).
The Supreme Court has not hesitated to strike down laws that impose economic burdens on speakers.19
In Minneapolis Star & Tribune Co. v. Minnesota Commissioner of Revenue, the Court invalidated a use tax on “paper and ink products consumed in the production of a publication.”20 This was a tax borne only by the press, and it only applied to a small subset of the press (publications that consumed more than $100,000 worth of ink and paper). Even though Minnesota did not impose an outright ban on specific content, the Court nonetheless found this economic burden, which applied differentially to the press, was unconstitutional.
Electricity is to a proof-of-work miner what paper and ink are to a newspaper publisher: a component consumed in the process of publishing. Like the use tax in Minneapolis Star & Tribune Co., the Moratorium imposes a financial burden by increasing the cost of “behind-the-meter electric energy consumed” in the publishing process, which burden is borne only by a specific category of speaker. And the Moratorium is even more “repugnant to First Amendment principles” than the use tax in Minneapolis Star & Tribune Co., because the Moratorium imposes its burden by drawing content-based lines.21
For that reason, the Moratorium bears similarities to a sales tax struck down in Arkansas Writers’ Project, Inc. v. Ragland, which taxed general interest magazines, but exempted newspapers, religious, professional, trade, and sports journals.22
In comparing the Arkansas sales tax to the use tax in Minneapolis Star & Tribune Co., the Court was particularly troubled by its content-based nature:
Indeed, this case involves a more disturbing use of selective taxation than Minneapolis Star, because the basis on which Arkansas differentiates between magazines is particularly repugnant to First Amendment principles: a magazine's tax status depends entirely on its content. Above all else, the First Amendment means that government has no power to restrict expression because of its message, its ideas, its subject matter, or its content. Regulations which permit the Government to discriminate on the basis of the content of the message cannot be tolerated under the First Amendment.23
Like the magazine tax in Ragland, whether the Moratorium applies to any particular protocol “depends entirely on its content.” Thus, and as argued more fully in the next section, the Moratorium’s content-based financial burden should be examined under the strictest scrutiny.
That Bitcoin miners are not part of the institutional press or mainstream media does not deprive them of the protections enjoyed by the newspaper and magazine publishers in the forgoing examples. The Supreme Court in Citizens United v. Federal Election Commission found such protections applied to a corporation formed to distribute political media, reiterating that:
We have consistently rejected the proposition that the institutional press has any constitutional privilege beyond that of other speakers. With the advent of the Internet and the decline of print and broadcast media, moreover, the line between the media and others who wish to comment on political and social issues becomes far more blurred.24
The Court also rejected arguments to diminish protections based on the medium used to publish speech. The Court declared it would not “draw, and then redraw, constitutional lines based on the particular media or technology used to disseminate political speech from a particular speaker,” which would have further chilling effects and amount to a violation of the First Amendment by the judiciary itself.25
It makes no difference to the First Amendment that Bitcoin miners use the Bitcoin protocol and proof-of-work algorithm, rather than newspapers, to publish information.
The state of New York might defend the Moratorium by minimizing the burden to proof-of-work miners as a “temporary” pause on new and increased contracts for carbon-based energy, not a permanent ban or burden on compensation.
But the Supreme Court rejected a similar temporal argument in Simon & Schuster, Inc. v. Members of the New York State Crime Victims Board, when it struck down a New York law requiring convicted criminals to escrow the proceeds of any sales of media depicting or recounting their crimes, in order to compensate victims.26
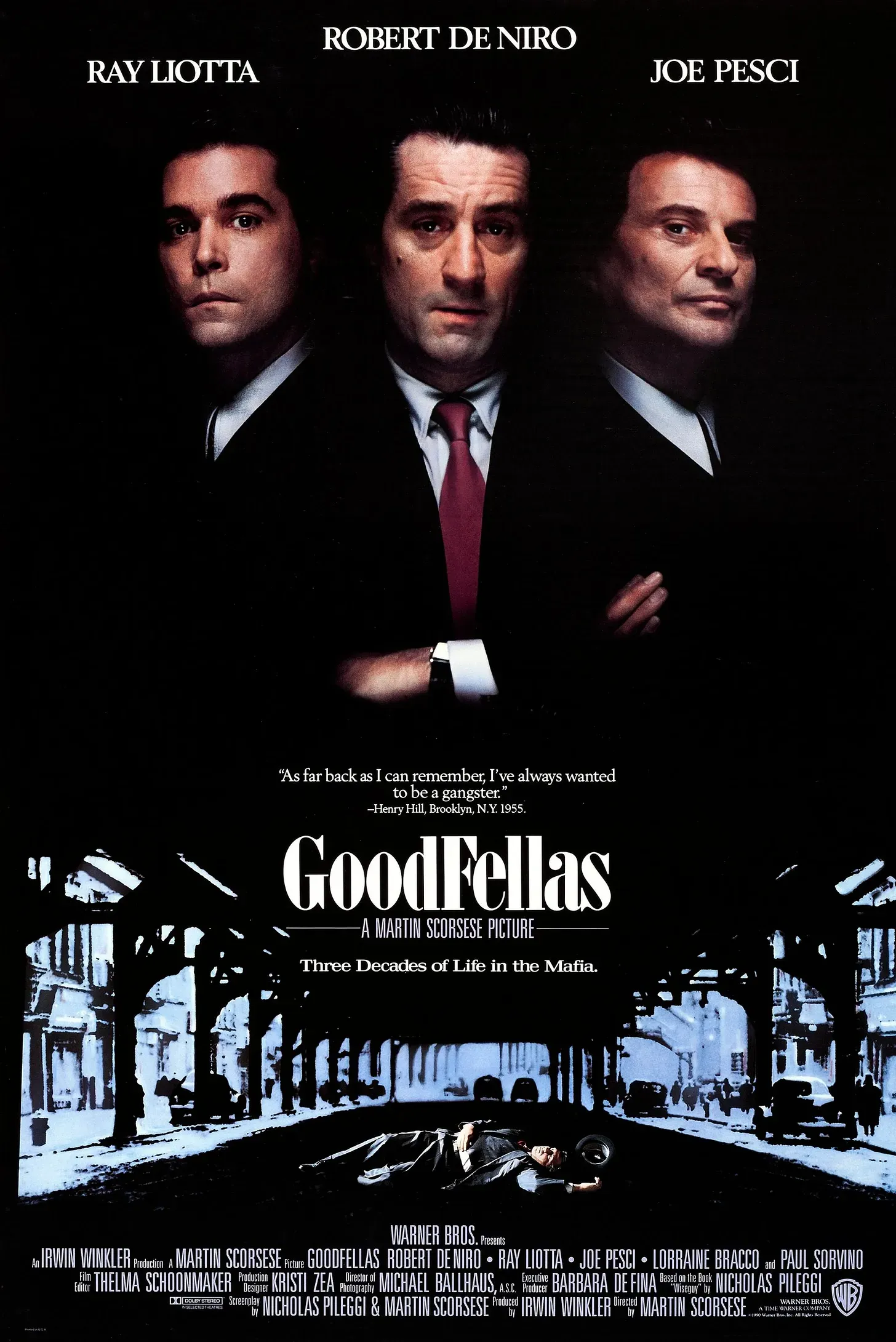
In Simon & Schuster, the publisher sued after New York enforced this law against it and Henry Hill, the infamous mobster-author of “Wiseguy,” an autobiography detailing Hill’s life as a “made man” for the New York mob (which Martin Scorsese turned into the Oscar-winning film “Goodfellas”).
New York tried to distinguish its escrow law from the tax in Ragland by emphasizing it did not confiscate funds outright, but held them for a period of time, after which, if no claims were made by victims, the funds would be returned to the author. The Supreme Court rejected this distinction out of hand, stating “this difference can hardly serve as the basis for disparate treatment under the First Amendment,” because both the escrow law and sales tax in Ragland were “forms of financial burden” that “operate[d] as disincentives to speak.”27
Likewise, here, the Moratorium may be temporary, but it nonetheless “operate[s] as [a] disincentive[] to speak.”28
Moreover, there is nothing preventing the “temporary” Moratorium from morphing into a permanent ban on the sale of “behind-the-meter electric energy consumed or utilized by cryptocurrency mining operations that use proof-of-work” by carbon-fuel-based electricity generators. (Indeed, a group of U.S. Senators recently has proposed just such a total ban on carbon-fuel-based energy to proof-of-work miners.)
The forgoing authorities demonstrate that the economic burdens imposed by the Moratorium are cognizable under the Supreme Court’s First Amendment jurisprudence.
The Moratorium Fails to Pass Any Level of Scrutiny Applied
Content-Based Regulations — Strict Scrutiny
The Moratorium imposes a burden on speech that is created as a result of, and in furtherance of, proof-of-work consensus protocols, but no other types of consensus mechanisms. It also specifically singles out two classes of speakers: (i) proof-of-work miners and (ii) carbon-fuel-based electricity providers that supply behind-the-meter electricity to those proof-of-work miners.
Thus, the Moratorium “imposes more than an incidental burden on protected expression. Both on its face and in its practical operation, [New York’s] law imposes a burden based on the content of speech and the identity of the speaker.”29
The Court recently reiterated the test for determining whether a regulation is content-based:
[A] law is content-based if a regulation of speech on its face draws distinctions based on the message a speaker conveys. That description applies to a law that singles out specific subject matter for differential treatment. For example, a law banning the use of sound trucks for political speech—and only political speech—would be a content-based regulation, even if it imposed no limits on the political viewpoints that could be expressed.30
The Moratorium undeniably “singles out specific subject matter” — proof-of-work algorithms — “for differential treatment.” No other cryptocurrency consensus mechanisms or algorithms are subject to the Moratorium’s freeze on carbon-fuel-based energy consumption. When determining whether to issue new or renewed air licenses to carbon-fuel-based energy providers, the Department of Environmental Conservation “must necessarily examine the content of the message that is conveyed” by any behind-the-meter cryptocurrency miners colocated at that energy provider.31
If the blocks published by miners colocated with the electricity provider contain solutions to proof-of-work algorithms and transaction data for cryptocurrency protocols secured by proof-of-work consensus mechanisms, the Department is prohibited from issuing the license.
“A statute is presumptively inconsistent with the First Amendment if it imposes a financial burden on speakers because of the content of their speech.”32
Accordingly, a “law that is content-based is subject to strict scrutiny.”33
Under strict scrutiny, the government bears the burden of proving:
- “its regulation is necessary to serve a compelling state interest,” and
- “is narrowly drawn to achieve that end.”34
Under this standard, laws are almost invariably declared unconstitutional. The highest level of scrutiny applies to content-based laws because:
Above all else, the First Amendment means that government has no power to restrict expression because of its message, its ideas, its subject matter, or its content. Regulations which permit the Government to discriminate on the basis of the content of the message cannot be tolerated under the First Amendment.35
Applying strict scrutiny, we first ascertain New York’s interest served by the Moratorium. The legislative findings included with the enacting bill identify “climate change” as a threat to the state. The bill continues, “[i]t is the policy of the State of New York to conserve, improve and protect its natural resources and environment and to prevent, abate and control water, land and air pollution.” And the bill identifies a concrete goal to reduce “statewide greenhouse gas emissions [by] … eighty-five percent by 2050 and that the state has net zero emissions in all sectors of the economy by that time.”
To be sure, the prevention of climate change and protection of the state’s natural environment are indeed weighty interests. There is little authority, however, on where this nebulous interest lies on the spectrum from “rational basis” (most deferential to government) to “compelling” (least deferential).
But even assuming for purposes of argument that climate change does present a compelling state interest, it is impossible for the state to prove that freezing greenhouse gas emissions at current levels from a single subset of only one industry is “narrowly drawn” to prevent climate change and protect the environment. Even if the state of New York froze all emissions within its borders, private and business-related, at current levels indefinitely, this would have negligible impacts on climate change. Climate change is a global phenomenon.
Nor is the Moratorium on proof-of-work cryptocurrency mining emissions narrowly drawn to achieve the state’s goal of reducing emissions by 85% by 2050 and rendering “all sectors of the economy” net-zero. Again, proof-of-work mining is but one subset of one industry within the New York economy.
There is no meritorious argument the state can marshal to rebut the presumption of unconstitutionality under a strict scrutiny analysis.
Commercial Speech — Intermediate Scrutiny
Proof-of-work data might also be considered commercial speech, as it could be argued that it “propose[s] a commercial transaction”
36 This is, of course, not accurate, as the transaction data published by miners is almost always between other parties involving transactions to which miners are not a party. Moreover, miners publish blocks that contain data beyond mere transactional facts, as previously established, including political opinions. Nevertheless, a judge operating with a superficial understanding of proof-of-work mining could reach for an easy heuristic like commercial speech.
But “even speech that does no more than propose a commercial transaction is protected by the First Amendment.”
37 Speech proposing a commercial transaction is, however, “entitled to lesser protection than other constitutionally guaranteed expression.”38
Commercial speech is regulated under intermediate or heightened scrutiny:
- the speech must relate to “lawful activity and not be misleading”;
- the governmental interest must be “substantial”; and
- the law must “directly advance[] the governmental interest asserted,” and not be “more extensive than is necessary to serve that interest.”39
In other words, “[t]here must be a fit between the legislature’s ends and the means chosen to accomplish those ends.”40
Proof-of-work miners, by their nature, publish truthful facts about transactions that are verified by the protocol’s network of nodes. This is a lawful activity and not misleading.
Thus, under intermediate scrutiny, the state will have to prove the Moratorium “directly advances” a “substantial interest.” Again, the law is unsettled on where general climate change and greenhouse emissions goals fall within the spectrum of governmental interests. But even under intermediate scrutiny, the state cannot show that its targeting of a single subset of one single greenhouse-gas-emitting industry “directly advances” its climate goals, for the reasons discussed above.
While this is an easier standard for the state to meet, the Moratorium is simply too underinclusive and ineffective at its stated goals to pass any level of scrutiny applied. Nonetheless, any action challenging the Moratorium should avoid classification of proof-of-work block publishing as pure commercial speech in order to establish a precedent securing the highest levels of protection.
Conclusion
Miners securing cryptocurrency protocols through proof-of-work algorithms, such as Bitcoin, are publishers engaged in speech entitled to First Amendment protections of the highest order. Because of this, any law or regulation affecting proof-of-work miners must be generally applicable and content-neutral. Laws such as the Moratorium in New York Assembly Bill A7389C, which target proof-of-work miners based on the content of their speech, violate miners’ First Amendment rights and should be invalidated.
Thus, the Moratorium (once signed into law) provides a meaningful opportunity for a test case to establish favorable precedent shielding the proof-of-work mining industry from burdensome regulation — and even outright bans. And, because the issue of whether the Moratorium is narrowly drawn to prevent climate change would be litigated in such a case, it would also provide an opportunity to dispel energy misinformation and FUD (Fear, Uncertainty, Doubt), based on credible expert testimony and judicial fact-finding. Such a case could shift the narrative on Bitcoin mining and demonstrate the incredible benefits proof-of-work protocols provide to society.
The goal of this article has been to spark thoughtful argument and debate on an important issue pertinent to Bitcoin and Constitutional rights. Please feel free to contribute to the discussion by commenting here, on twitter, or by email.
Until next time,
Aaron
See Satoshi Nakamoto, Bitcoin: A Peer-to-Peer Electronic Cash System 2 (2008), https://bitcoin.org/bitcoin.pdf (last visited June 21, 2022) (emphasis added).
Andreas Antonopoulos, The Internet of Money, Vol 2.
Nakamoto at 2.
Id. at 3.
Andreas Antonopoulos, Mastering Bitcoin 173 (2015).
Yan Pritzker, Inventing Bitcoin: The Technology Behind the First Truly Scarce and Decentralized Money Explained 25 (2019)
Mastering at 26.
Pritzker at 27.
Mastering at 180
Id. at 183-85
Id. at 185.
Mastering at 181.
See also W. Aaron Daniel, The Constitutional Argument for State Adoption of Bitcoin as Legal Tender (Part IV of IV): Bitcoin’s Faustian Bargain (May 2, 2022) (arguing the genesis block’s coinbase data was a political statement, as well as a timestamp).
The Bitcoin BriefThe Constitutional Argument for State Adoption of Bitcoin as Legal Tender (Part IV of IV)This is the fourth post in a four-part article exploring the constitutionality of state-level Bitcoin legal tender laws — and the philosophical arguments against such laws. Each part will be released weekly by separate post, and all parts will ultimately be collected in a final post with the full article…Read morea year ago · W. Aaron Daniel14
Sorrell v. IMS Health Inc., 564 U.S. 552, 570, (2011) (law restricting sale of prescribing-doctor data for marketing purposes was unconstitutional).
Id.
Id. at 570.
Sorrell, 564 U.S. at 566 (citing Simon & Schuster, Inc. v. Members of N.Y. State Crime Victims Bd., 502 U.S. 105, 115 (1991); Minneapolis Star & Tribune Co. v. Minnesota Comm'r of Revenue, 460 U.S. 575 (1983)).
https://legislation.nysenate.gov/pdf/bills/2021/A7389C
See, e.g., Minneapolis Star & Tribune Co., 460 U.S. at 593 (tax on newspaper publishers’ use of ink and paper violated the First Amendment); Simon & Schuster, Inc., 502 U.S. at 115 (law impounding income derived from sale of convicted criminals’ memoirs imposed impermissible “financial burden” on both publishers and authors); Ark. Writers' Project, Inc. v. Ragland, 481 U.S. 221, 227, 107 S. Ct. 1722, 1727 (1987) (sales tax that applied to general interest magazines, but exempted newspapers and religious, professional, trade, and sports journals “burden[ed] rights protected by the First Amendment”); U.S. v. Nat'l Treasury Employees Union, 513 U.S. 454, 468 (1995) (law preventing government employees from earning honoraria for speeches, appearances, or articles was unconstitutional; law’s “prohibition on compensation unquestionably impose[d] a significant burden on expressive activity”).
460 U.S. at 577.
Ragland, 481 U.S. at 229-30.
481 U.S. at 223.
Id. at 229-30 (emphasis added; internal quotation marks and citations omitted).
Citizens United v. Fed. Election Com'n, 558 U.S. 310, 352 (2010) (internal citations and quotation marks omitted; emphasis added).
Id. at 326.
502 U.S. at 117.
502 U.S. at 116–17.
Id.
Sorrell., 564 U.S. at 567.
Barr v. Am. Ass'n of Political Consultants, 140 S. Ct. 2335 (2020).
Ragland, 481 U.S. at 230.
Simon & Schuster, 502 U.S. at 115 (applying strict scrutiny).
Barr, 140 S. Ct. at 2347 (internal quotation marks and citation omitted).
Simon & Schuster, Inc., 502 U.S. at 118.
Ragland, 481 U.S. at 229-30 (internal citation and quotation marks omitted).
Cincinnati v. Discovery Network, 507 U.S. 410, 421 (1993).
Id. at 421.
Id. at 422.
Central Hudson Gas & Elec. Corp., v. Public Service Comm'n., 447 U.S. 557, 566 (1980) (setting forth separate constitutional standard for regulations impacting commercial speech)).
Sorrell, 564 U.S. at 572 (“[T]he State must show at least that the statute directly advances a substantial governmental interest and that the measure is drawn to achieve that interest.”).